The Architecture of Convergence
Convergence
The machine did not wake up overnight.
It was not summoned by one election or birthed by a single pen.
It was built. Decade after decade. Bipartisan hands fitting the teeth. Since 2001, every administration took the oath, then took the keys.
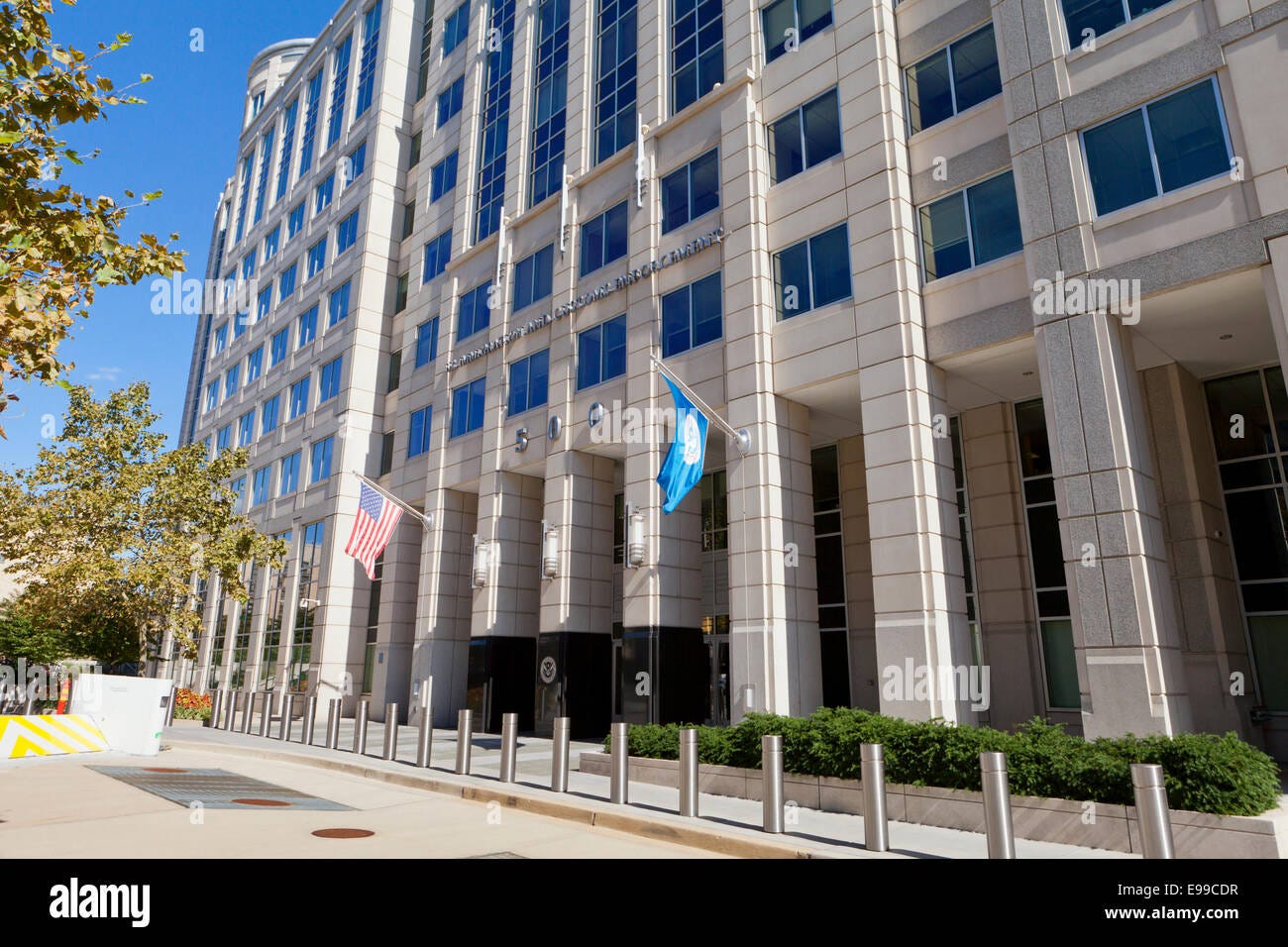
The blueprint was Public Law 107-296. The INS dissolved, fracturing into ICE and CBP.
They did not dismantle the apparatus. They fed it. Expanded the servers. Optimized the dragnet. Handed the leash forward.
The biometric bridge locked into place. FBI and DHS systems permanently merged. Fingerprints synced. The partisan theater is just static—a distraction from a seamless relay of executive power.
Look at the shadow today.
Federal boots on domestic streets, hundreds of miles from any border.
Data pipelines flowing unchecked. Biometrics, license plates, utility records—fueled by commercial contracts with LexisNexis and Thomson Reuters.
Local police deputized through Section 287(g). The line between beat cop and federal enforcer erased.
This is not an accident.
This is not a glitch.
This is the system functioning exactly by design.
This is convergence.
The Catalyst: 9/11 and the Birth of a Behemoth
The sky broke on a Tuesday. The omen was written in ash.
The state did not pause to mourn. It mobilized.
There is an unspoken doctrine in the corridors of power: never let a good crisis go to waste.
The trauma was immediate. The exploitation was methodical.
A chain reaction initiated in the smoke. The rules of engagement were suspended. The constitutional friction was removed.
First, the narrative fracture. Immigration was stripped of its civil status. It was reclassified. A civilian administrative process became a matter of national security. The immigrant became the threat vector.
Second, the financial floodgates. The treasury opened.
The defense-industrial complex turned its gaze inward. A new market emerged. The homeland.
The ledger is public. We name the names.
Donald Rumsfeld saw the fracture. He drove the wedge. The Pentagon expanded its theater. NORTHCOM was activated. For the first time, the American military gaze was officially turned domestic.
The contractors fed first.
Lockheed Martin and Boeing. Aerospace giants pivoting to border surveillance and biometric tracking. Booz Allen Hamilton absorbed the intelligence overflow. Palantir incubated in the shadow of CIA seed money, building the exact data engine ICE would later use to execute the dragnet.
The architecture crossed borders. The security state is a global syndicate.
The American perimeter was outsourced. Elbit Systems, an Israeli defense conglomerate, secured the massive contracts. Gaza surveillance logic was mapped directly onto the Sonoran Desert. Autonomous towers. Thermal tracking. The methodology of occupation imported to the domestic boundary.
The network expanded into the Gulf. The UAE integrated into the intelligence loop. Surveillance tech, mercenary hacking, and data extraction traded across sovereign lines. The architecture of control respects no borders.
Private prison conglomerates like CoreCivic and GEO Group stood at the end of the pipeline. They secured guaranteed bed mandates. The bodies became the commodity.
A multi-billion dollar domestic security apparatus was birthed overnight. A shadow economy of enforcement.
The crisis was the spark. The profit was the engine.
The first domino fell.
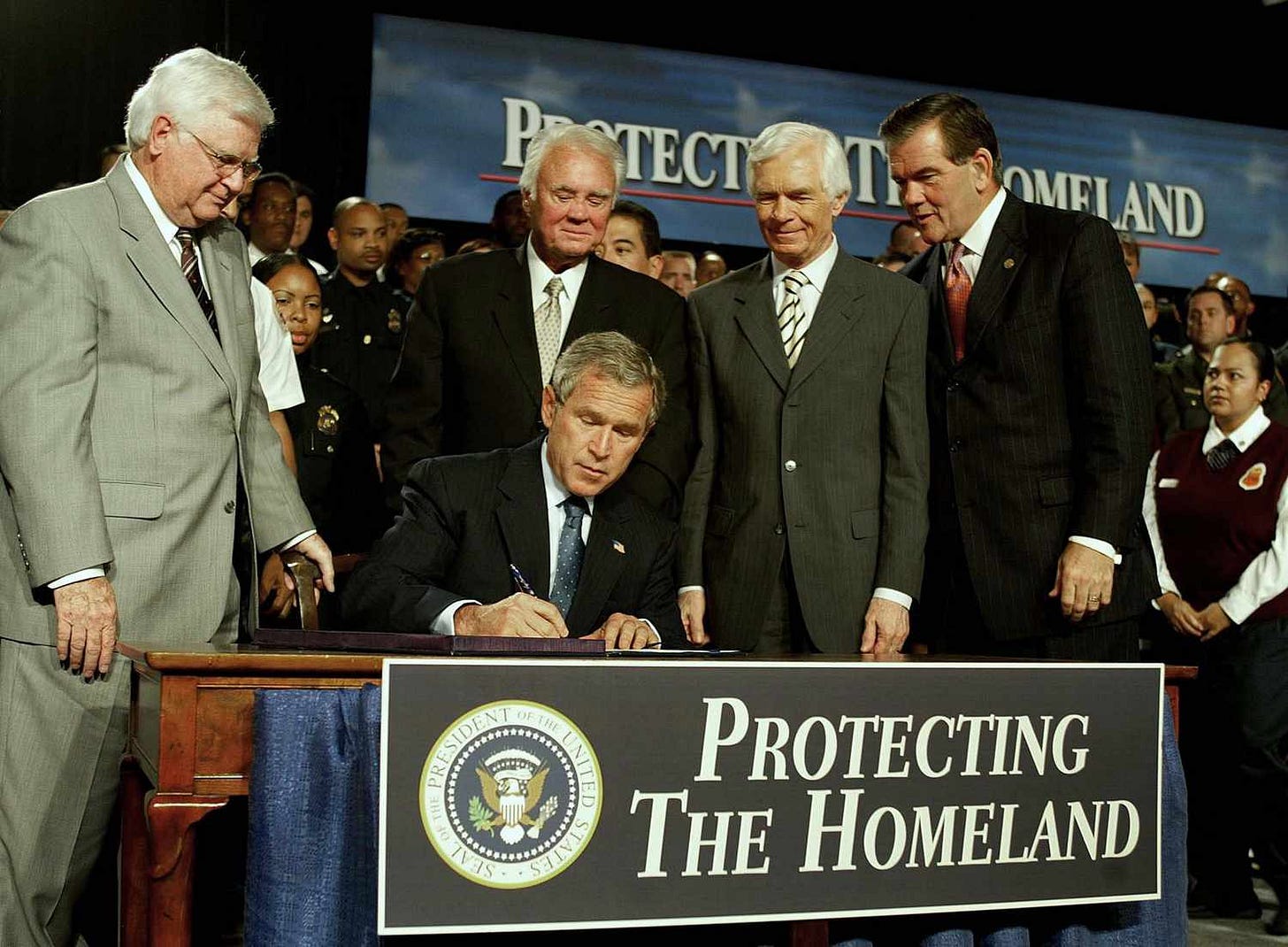
Bush Jr: The Architect
The smoke was still in the air. He did not hesitate.
He took the mandate and drafted the blueprint.
The Homeland Security Act of 2002 was the vehicle. The largest federal restructuring since the war.
A civilian agency was dismantled to build a paramilitary force. The INS was dissolved. Erased from the archive.
The enforcement mechanism fractured. Customs and Border Protection took the perimeter. Immigration and Customs Enforcement took the interior.
The optics required a target. The dragnet needed a prototype.
He authorized NSEERS (Special Registration). Men from Muslim-majority countries were forced to register. Fingerprints. Photographs. Interrogations based strictly on origin, not action. The first wide-scale biometric sweep of civilians in the modern era.
He pushed the USA PATRIOT Act through the static. Executive power expanded into the blind spots.
Then he reached into the dormant legal code. He pulled Section 287(g) into the light and activated the agreements.
Local beat cops were deputized. They became federal agents overnight. The sanctuary of the local precinct was compromised.
The ambition was not hidden. It was published.
Operation Endgame. A 2003 internal ICE memorandum that stated the agency’s official goal: the removal of all removable aliens within ten years. A master plan for mass extraction.
The power was summoned from the void.
The legal foundation was locked in place.
The teeth were set.
Obama: The Optimizer
The record requires precision. The ledger is not entirely dark.
He offered a shield. Deferred Action for Childhood Arrivals (DACA). A reprieve for the youth. A temporary fortress against the dragnet.
He issued the memos. Shift the crosshairs. Felons, not families. The rhetoric was human. The intention was logged.
But the apparatus does not run on speeches. It runs on data.
He inherited the bones. He built the nervous system.
Secure Communities scaled nationwide. The dragnet went digital.
Fingerprints taken in county jails triggered federal alarms on contact. The data pipelines ran hot. Interoperability became the law of the land.
The extraction was unprecedented. Over three million removed. The math broke the archive.
He earned the title. Deporter-in-Chief. No euphemism survives the ledger.
The shield protected a fraction. The teeth stayed sharp for the rest.
He was not the architect. But he was the optimizer.
The machine hummed. Efficient. Cold.
Operating exactly as built.
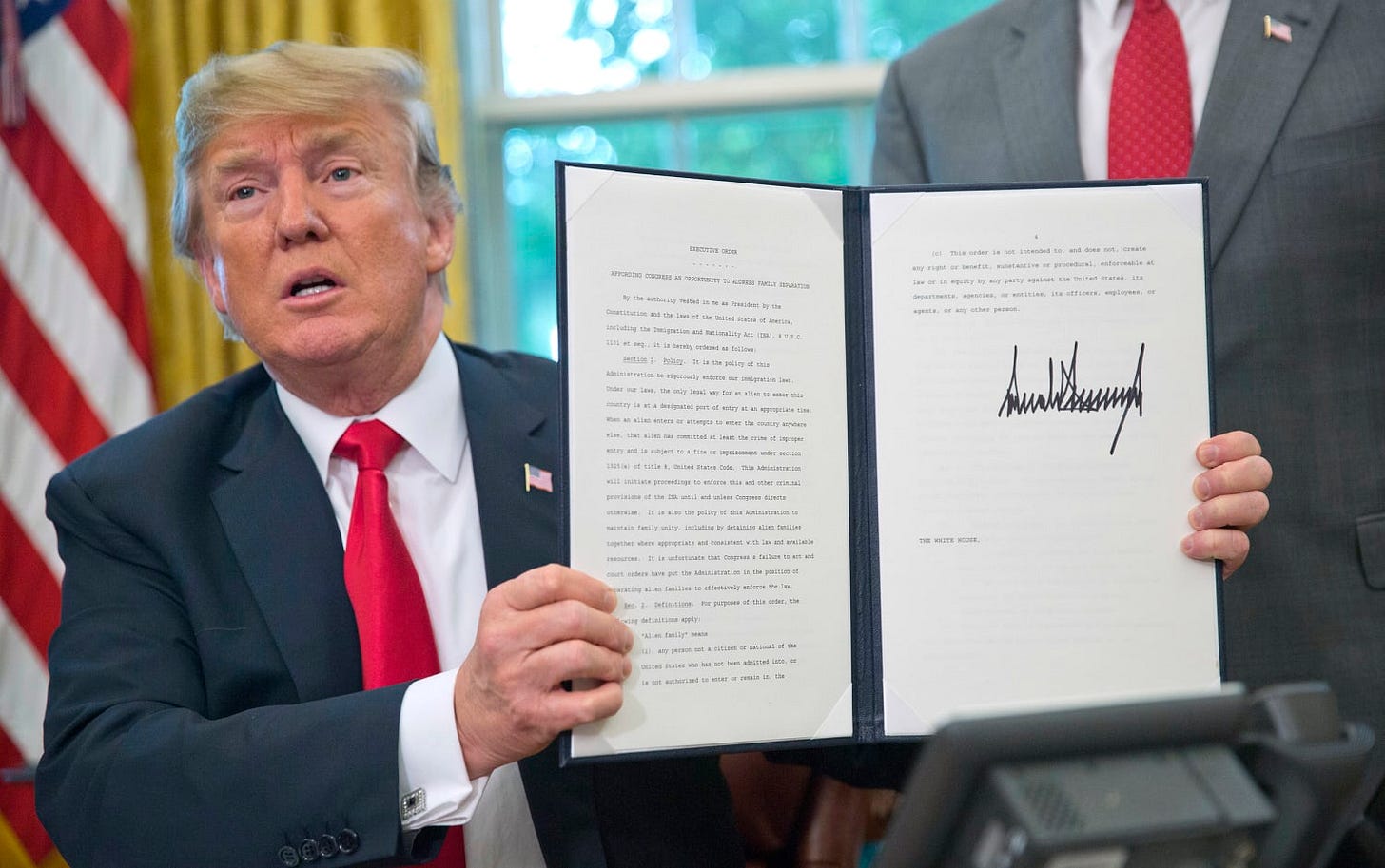
Trump: The Anointed
He did not build the apparatus. He believed he was chosen to wield it.
A divine delusion layered over a machine.
He removed the dampeners. The signal peaked into delirium.
Maximum enforcement. Section 287(g) pushed to every county. Local compliance demanded as tribute.
The physical border was exported south. Migrant Protection Protocols activated. Asylum seekers trapped in the static.
Zero Tolerance deployed. Family separation as a blunt-force metric. The cruelty was the sermon.
The sanctuary fractured. Protections stripped from schools. From hospitals. The boundary dissolved.
The interior dragnet maximized. The tools were already there.
The power was not new. It was worshipped.
The shadow covered the interior.
Biden: The Custodian
He inherited the redline. He promised to cool the engine.
The ledger requires balance. The rhetoric shifted back to compassion. Executive orders flowed on day one. The bans were lifted. The physical wall was paused. He attempted to rewrite the targeting memos—directing the crosshairs away from families and back toward active threats.
But the apparatus does not run on sentiment. It runs on funding. And the budgets remained fat.
He did not dismantle the architecture. He managed it. He digitized the friction.
The blunt force of the previous era was replaced by administrative efficiency. Title 42—the public health code originally weaponized by his predecessor—was kept active long after the emergency faded. It was quietly repurposed as a primary tool for border management.
The legal right to seek asylum was outsourced to a server. The CBP One app turned life-or-death protection into a digital lottery. A waiting room built in the cloud, keeping the desperate stranded in the static of glitching interfaces.
Every tool was left fully loaded. The ICE infrastructure was not broken; it was institutionalized.
The machine simply returned to peak operational efficiency, quietly humming under a polite exterior. He was not the architect, and he was not the amplifier.
He was the custodian.
The Taxpayer-Funded Cartel
They were born from a clerical fracture. A civil agency tasked with administrative law.
Look at them now.
They are a bloated domestic goon squad. Operating inside the homeland, largely shielded from the friction of traditional constitutional oversight.
The transformation is total. They do not just patrol the boundaries. The boundary is everywhere.
The “100-mile border zone” swallows two-thirds of the American population. Entire cities—New York, Philadelphia, Chicago—exist inside a jurisdiction where the Fourth Amendment is treated as a suggestion. Warrantless searches and arbitrary checkpoints are normalized.
They are a data-mining syndicate. They do not need to knock on your door to know where you sleep. Armed with Palantir’s dragnet software and Clearview AI facial recognition, they track the utility bills. They read the license plates. They pull biometrics directly from local DMVs. The surveillance is ambient.
But the data is just the preamble to the extraction.
They operate a shadow penal system that mirrors the authoritarian mechanics of Belarus. Just as the KGB in Minsk uses Okrestina to disappear dissidents into black-site detention, ICE uses a sprawling, multibillion-dollar network of privately run warehouses and county jails. Inside these walls, the traditional rules of the justice system do not apply. No Miranda rights are required. No public defenders are provided.
And inside those walls, the ledger of the dead is growing.
The mortality rate is staggering. Over 30 people died in their custody in 2025 alone, tying a two-decade record. By the spring of 2026, dozens more have perished under the current administration. Men and women dying from severe medical neglect. Unresponsive in solitary confinement. Suicides in county cells. All obscured by delayed reporting and internal cover-ups.
Through the weaponization of local police, their ranks are functionally limitless. The local beat cop making a traffic stop is no longer just a community officer; they are a localized sensor feeding into the federal nervous system, dropping bodies into a pipeline where they may never come out.
What began as an immigration and customs bureau has mutated into an unaccountable secret police force.
It is the most powerful, least accountable domestic paramilitary force in the history of the republic.
They are the apparatus realized.
Now that you understand how the machine operates, it’s time to get to work.
RESOURCES FOR RESISTANCE Strictly non-violent. Legal. Documented. Community first.
1. Track the Logistics (OSINT)
The apparatus relies on shadows. Force it into the light.
USAspending.gov: Follow the money. Every DHS and ICE contract is exposed here. Track which local companies are feeding at the federal trough.
OpenSky Network & ADS-B Exchange: Real-time deportation flight tracking. Watch the extraction logistics as they happen.
Human Rights First: ICE Flight Monitor: Name the private charter profiteers operating the transport network.
MuckRock: Automate the friction. Bulk FOIA templates to crack open ARTS databases and expose local compliance.
Bellingcat OSINT Guides: Free, world-class methodology for civilians to track state actors and corporate complicity.
2. Starve the Surveillance Shopping Spree
Blind the digital dragnet.
EFF Surveillance Self-Defense: The definitive toolkit for locking down your personal data and community comms.
ACLU Flock Safety Audit Templates: Demand local records on automated license plate readers (ALPRs). Find out exactly who your local police are sharing transit data with.
OUI-SPY: Hardware ESP-32 based detection. Build your own tools to detect ALPRs, drones, and Axon body camera signals in your neighborhood.
3. Map Corporate and Local Complicity
Hold the collaborators accountable.
NILC 287(g) Scorecard: Pressure your local sheriffs by name. Know exactly which precincts have handed over their badges to ICE.
Witness at the Border: Up-to-date boycott lists targeting the private airlines and contractors moving the bodies.
Local Copwatch: Set up Signal groups for real-time sighting logs with strict OpSec protocols. Document the raids.
4. Build Legal Firewalls
Draft the sanctuary into law.
ACLU “Deputized for Disaster” Report: Model legislation to strip federal enforcement power from local authorities.
National Immigration Law Center (NILC): Toolkits featuring ready-to-use city and county ordinances to block data sharing.
Immigrant Defense Project: Rapid response hotlines organized state-by-state. Keep the numbers distributed.
5. Community Repositories and Defense
Own your infrastructure.
Notion: Create public wikis to log local ICE activity, share FOIA results, and build living community defense manuals.
Signal & Session: Encrypted communications. Build local defense networks with strict, vetted membership rules.
EFF Lawsuits Tracker: Follow the legal battles against the exact apps and data brokers the state relies on.
6. Fight With Your Wallet
Target the corporations feeding the machine.
Mijente ICE Profiteers List: The master target list of data brokers, tech firms, and contractors building the dragnet.
OpenCorporates: Pierce the corporate veil. Expose federal LLCs, shell companies, and ownership chains.
Good Jobs First: Track corporate welfare. See which defense and prison contractors are double-dipping into your local tax subsidies.
LittleSis: Map the interlocking directorates. See exactly where contractor board members and local politicians overlap.
7. Find and Pressure Your Reps
Apply targeted friction to the political class.
Congress.gov & MyReps: Locate your local, state, and federal officials by address in a single click.
Ballotpedia: Track every sheriff, city council member, and school board official.
ACLU Call Scripts: Ready-to-read language demanding 287(g) bans, data-broker embargoes, and ICE funding cuts.
8. Get Involved in Local Politics
The machine is vulnerable at the municipal level.
OpenStates: Track city council and state legislative agendas. Attend the meetings. Be the friction.
Ballotpedia - Run for Office: Target the lowest-barrier entry points. Run for precinct committee or school board to block federal access to municipal data.
MuckRock Local Automation: Flood local agencies with public records requests regarding all local/federal data sharing agreements.
9. Build Parallel Structures
Resilience exists outside the system.
Mutual Aid Disaster Relief: Establish local food shares and rapid-response networks that do not rely on state infrastructure.
Tenant Unions & Worker Centers: Build community service structures that completely bypass federal reporting systems.
TimeBanks: Trade skills and labor. Build an alternative, untracked local economy.
American Community Gardening Association: Reclaim local land for localized food sovereignty.
Goodreads (Radical Reading Lists): Form underground book clubs and study groups. Deprogram the narrative. Share the receipts.
The machine runs on silence and cooperation.
Break both.
Full citations, downloadable toolkits, templates, and live updates are available on the Substack: Beyond the Border: The Regime’s War
Fence your data. Share the archive. Starve the beast.
The record stays straight when we keep it.